Blog Posts
Where Do Deleted Files Go?
Deleting a file doesn’t erase it—learn where your data really goes, how to recover it, and how to safely delete it for good.
Tips to Get the Most Out of Your Microsoft 365 Apps
Unlock your team’s potential with Microsoft 365—collaboration, automation, and security all in one powerful platform.
New Gmail Threats Targeting Users in 2025 and How to Stay Safe
AI-powered scams are rising in 2025. Learn how to secure your Gmail account and protect your digital life with our expert tips.
7 New and Tricky Types of Malware to Watch Out For
From fileless to polymorphic, today’s malware is more dangerous than ever. Learn 7 threats and how to protect your digital life.
How Much Device Storage You Need
Running out of storage slows performance. Learn how to choose the right amount, manage space, and avoid storage issues on your device.
Is it Time for a Device Upgrade?
Slow, outdated device? Poor battery, crashes, or missing updates? Here are 7 signs it’s time to upgrade for better performance.
Spotting the Difference Between Malware and Ransomware
Malware steals data, ransomware locks files for ransom. Learn how to spot, prevent, and respond to these growing cyber threats.
Top 10 Security Tips for Mobile App Users
3 out of 4 apps have security flaws. Learn how to stay safe with these 10 essential mobile security tips.
8 Considerations Before Buying Used Technology
Buying used tech can save money, but it requires caution. Check support, battery health, and damage before making a purchase.
6 Ways to Organize Your Devices for Productivity
Boost productivity by organizing your device! Declutter apps, manage files, streamline emails, and optimize passwords. Small changes lead to big efficiency gains.
10 Steps to Prevent a Data Breach
Prevent data breaches with strong passwords, encryption, and regular updates. Train employees and limit access. Stay vigilant—protect your business today!
Ways Using AI for Work Can Get Complicated
AI can help at work, but it’s not perfect. Verify its outputs, stay updated on AI laws, and keep humans in charge of key decisions. Use AI wisely!
How to Minimize Ransomware Damage
Protect yourself from ransomware by keeping software updated, using antivirus, avoiding suspicious emails, and backing up files. Need help? Contact us today!
Best Practices for Secure Data Backup
Protect your data with regular backups! Use the 3-2-1 rule: 3 copies, 2 media types, 1 offsite. Need help setting up backups? Contact us today!
5 Common Cyber Threats and How to Avoid Them
Cyber threats are rising. Stay secure with strong passwords, 2FA, and caution online. For tips or help after an attack, contact us today!
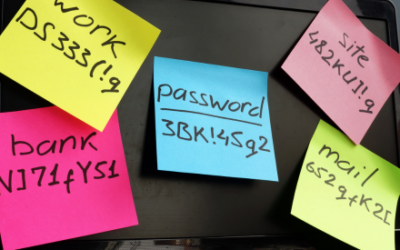
Can Password Managers be Hacked?
Password managers provide a convenient and secure way to store and manage your passwords. While no system is completely foolproof, strong encryption, two-factor authentication (2FA), and user diligence can significantly minimize risks. Always choose a reputable manager, use a strong master password, and stay updated to ensure optimal protection for your online accounts.
10 AI Tools You Need in Your Office for Productivity
AI tools are transforming the workplace, boosting productivity through smarter time management, enhanced communication, efficient data analysis, creative support, and improved customer service.
What is Blockchain Technology and How Does it Work?
Blockchain is a secure, decentralized digital ledger that stores information in linked blocks. It powers cryptocurrencies and has potential in many industries.
Ultimate Guide to Encryption Methods
Encryption keeps your data secure by converting it into unreadable code. Learn how encryption methods like AES and RSA protect your privacy every day.
What is Threat Exposure Management?
Stay ahead of cyber threats with Threat Exposure Management (TEM). Spot, fix, and prevent weak spots in your network for stronger, smarter security today.
Tips For a Seamless Smart Home Experience
Transform your home with smart tech! From hubs to smart lights, unlock convenience, safety, and fun. Learn how to build and secure your smart home today.
Innovative Solutions to IoT Device Security
IoT is growing, but so are security risks. Learn how strong passwords, updates, encryption, and new tech like AI and blockchain can keep your devices safe.
How Password Managers Protect Your Account
Password managers securely store and generate strong passwords, simplifying online safety and protecting your accounts with ease. Secure your digital life today!
How is Your Cyber Hygiene?
Cyber hygiene is your online self-care. Use strong passwords, update software, and back up data to stay safe from hackers in 2025. Protect your digital life!
Do You Really Need Dark Web Monitoring?
Dark web monitoring protects your data by detecting stolen info like passwords and credit cards, helping you act quickly to secure your identity.
Watch Out for Google Searches – Malvertising is on the Rise
Malvertising, or malicious online ads, exploits platforms like Google and social media to mislead users into clicking harmful links or visiting fraudulent sites. To stay safe, scrutinize URLs, visit sites directly, use DNS filters, avoid logging in or downloading from ads, and ignore suspicious phone numbers. Stay informed and share knowledge to enhance cybersecurity awareness.
8 Steps to Take When You Get a Notice Your Data was Breached
Data breaches are common, exposing sensitive info like SSNs or credit card details. Protect yourself: verify breach notices, update passwords, enable MFA, monitor accounts, freeze credit, review notifications, secure devices, and stay alert for phishing.
How Can Small Businesses Embrace the Cashless Revolution
Cashless payments are the future. With wallets like Apple Pay and Google Pay in demand, small businesses must adapt to stay competitive. Benefits include faster transactions, enhanced security, and better customer experiences. Go cashless to thrive!
Guide to Smart Windows 11 Settings to Boost Your Productivity
Windows 11 is gaining traction, with over 31% market share as of August 2024. Upgrade and maximize productivity with features like customizable Start Menus, Snap Layouts, Virtual Desktops, and Focus Assist. Unlock the full potential of your workflow!
5 New Trends from a Study on the State of AI at Work
AI is transforming workplaces, boosting efficiency, and driving growth. With 75% of workers using AI, businesses must adopt it thoughtfully, upskill teams, and address ethics like transparency and privacy to unlock potential and stay competitive.